The SSH protocol is widely used to securely access Linux servers. Most users connect securely to the remote server using the default SSH connection. However, vulnerable default configurations can compromise security as well.
The root account of a server with open SSH access can be at risk. Especially if you are using a public IP address, it is much easier to crack the root password. Therefore, it is necessary to understand SSH security.
Here’s how to secure SSH server connections on Linux.
1. Disable root user login
To do this, first, disable SSH access for the root user and create a new user with root privileges. Closing server access for the root user is a defensive strategy that prevents attackers from achieving their goal of breaking into the system. For example, you can create a user named example root as follows: copy
useradd -m exampleroot
passwd exampleroot
usermod -aG sudo examplerootHere is a brief description of the above command:
- useradd creates a new user, and the -m parameter creates a folder under the home directory of the user you created.
- The passwd command is used to assign a password to a new user. Remember that the passwords you assign to users should be complex and difficult to guess.
- usermod -aG sudo adds the newly created user to the administrators group.
After the user creation process, some changes need to be made to the sshd_config file. You can find this file at /etc/ssh/sshd_config. Open the file with any text editor and make the following changes: copy
# Authentication:
#LoginGraceTime 2m
PermitRootLogin no
AllowUsers exampleroot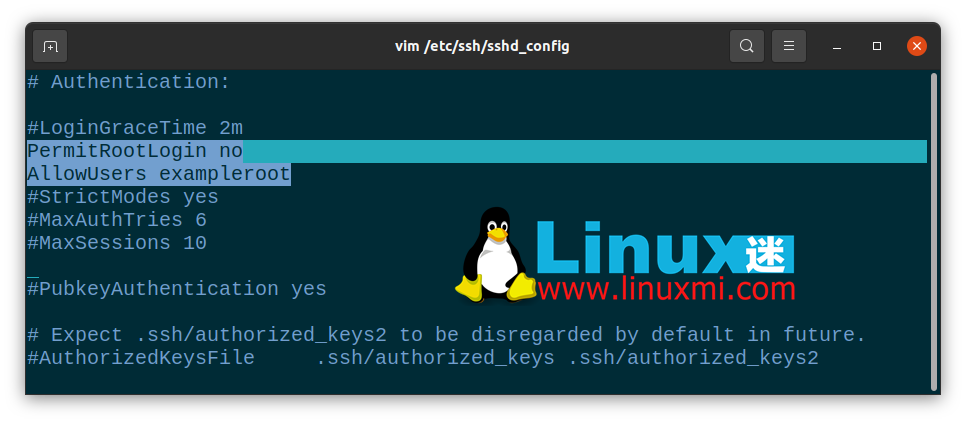
The PermitRootLogin line will prevent the root user from gaining remote access using SSH. Including exampleroot in the AllowUsers list grants the necessary permissions to the user.
Finally, restart the SSH service with the following command:copy
linuxmi@linuxmi /home/linuxmi/www.linuxmi.com
⚡ sudo systemctl restart sshIf it fails and you get an error message, try the following commands. This may vary depending on the Linux distribution you are using.copy
linuxmi@linuxmi /home/linuxmi/www.linuxmi.com
sudo systemctl restart sshd2. Change the default port
The default SSH connection port is 22. Of course, all attackers know this, so the default port number needs to be changed to secure SSH. While attackers can easily find new port numbers with an Nmap scan, the goal here is to make the attacker’s job more difficult.
To change the port number, open /etc/ssh/sshd_config and make the following changes to the file:copy
Include /etc/ssh/sshd_config.d/*.conf
Port 22099
After this step, restart the SSH service again with sudo systemctl restart ssh. Now you can access your server using the port you just defined. If you are using a firewall, you must also make the necessary rule changes here. When running the netstat -tlpn command, you can see that your SSH port number has changed.
3. Block access to users with blank passwords
There may be users on your system that you accidentally created without passwords. To prevent such users from accessing the server, you can set the value of the PermitEmptyPasswords line in the sshd_config file to no.copy
PermitEmptyPasswords no4. Limit login/access attempts
By default, you can try entering your password as many times as you want to access the server. However, an attacker could exploit this vulnerability to brute force the server. By specifying the number of password attempts allowed, you can automatically terminate the SSH connection after a certain number of attempts.
To do this, change the MaxAuthTries value in the sshd_config file.copy
MaxAuthTries 35. Using SSH version 2
The second version of SSH was released because there were many vulnerabilities in the first version. You can enable the server to use the second version by default by adding the Protocol parameter to the sshd_config file. This way, all your future connections will use the second version of SSH.copy
Include /etc/ssh/sshd_config.d/*.conf
Protocol 2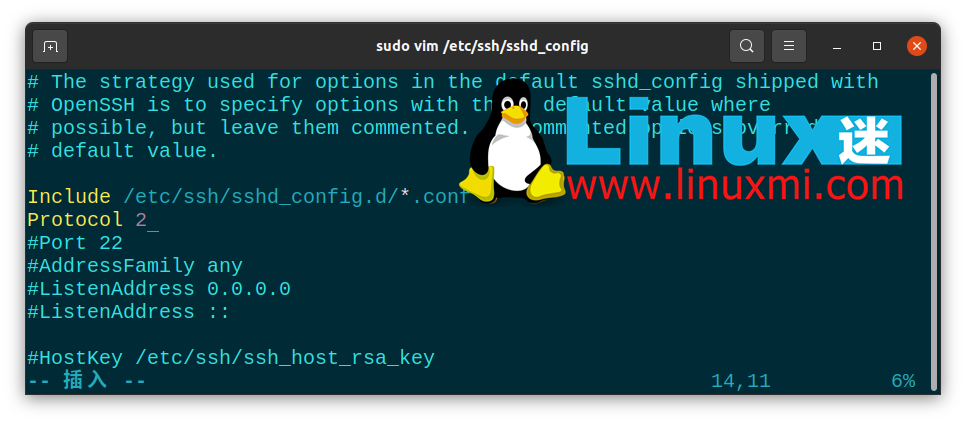
6. Disable TCP port forwarding and X11 forwarding
Attackers can try to access your other systems through port forwarding of SSH connections. To prevent this, you can turn off the AllowTcpForwarding and X11Forwarding features in the sshd_config file.copy
X11Forwarding no
AllowTcpForwarding no7. Connect using an SSH key
One of the safest ways to connect to a server is to use an SSH key. When using SSH keys, you can access the server without a password. Alternatively, you can turn off password access to the server entirely by changing password-related parameters in the sshd_config file.
When creating an SSH key, there are two keys: Public and Private. The public key will be uploaded to the server you are connecting to, while the private key will be stored on the computer you will be using to establish the connection.
Create an SSH key on your computer using the ssh-keygen command. Do not leave the passphrase field blank and remember the password you enter here. If you leave it blank, you will only be able to access it using the SSH key file. However, if you set a passphrase, you can prevent an attacker who has the key file from accessing it. For example, you can create an SSH key with the following command:copy
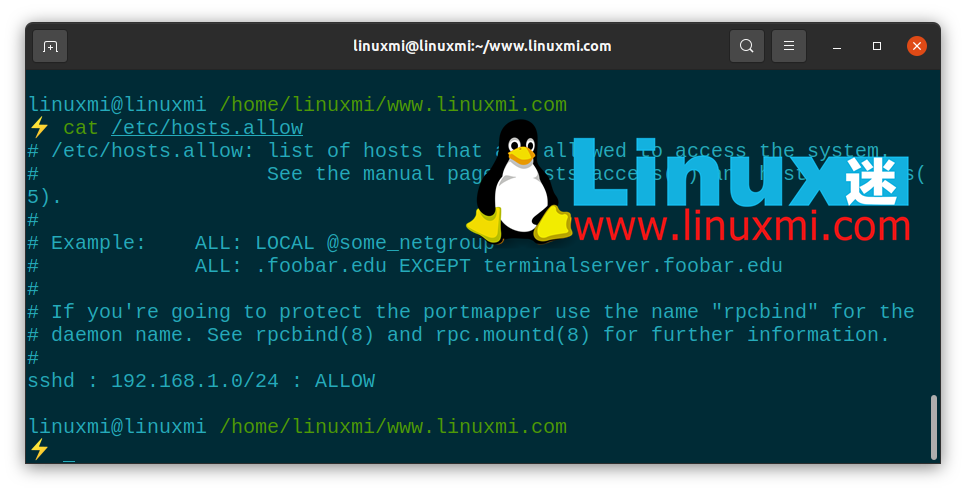
ssh-keygen8. IP Restrictions for SSH Connections
Most of the time, firewalls block access using their own standard framework, designed to protect servers. However, this is not always enough and you need to increase this security potential.
To do this, open the /etc/hosts.allow file. With additions to this file, you can restrict SSH permissions, allow specific IP blocks, or enter a single IP and block all remaining IP addresses with the deny command.
Below you will see some sample settings. After doing this, restart the SSH service as usual to save the changes.
The Importance of Linux Server Security
All server administrators should consider data and data security issues. Server security is a very sensitive issue because the main focus of attacks are web servers, which contain almost all information about the system. Since most servers run on Linux infrastructure, it is important to be familiar with Linux systems and server administration.
SSH security is just one of the ways to protect your server. You can minimize the damage you take by stopping, blocking, or slowing your attacks. In addition to providing SSH security, you can implement many different methods to secure your Linux server.